Zeros and ones
I once was sitting on a bench in a park, long ago
An old man was next to me on the bench, and we got talking. When I told him
that I worked in computing he said "I've heard they only use 0s and 1s".
And that got me thinking: on one level it is true, but it misses an
important point.
Bricks
And so I explained to him that while it is true on one level, that there was
another way to see it.
You could equally say "A house is only made of bricks." Again, it is true,
but the bricks are used to make walls, the walls to make rooms, and the rooms
to make a house.
You could even say "A brick is made of grains of sand" and therefore
conclude that houses are 'only' made of sand.
Internet layers
The internet is layered in a similar way. (What follows is a
simplification)
At the lowest level you have wires carrying electricity at changing voltage.
One voltage, within certain tolerances, represents 0, and another voltage
represents 1.
Bits
The next level up only has to worry about those zeros and ones, it doesn't
have to worry about voltages, and thinks it is just sending zeros and ones
across the wires.
Reliability
However, these zeros and ones may not get sent entirely faithfully, and
sometimes a bit gets flipped, or one gets inserted or deleted, for instance
because of noise on the line.
So a higher level is involved in getting those bits sent reliably. A long
'message' gets split into packets, and numbered, and sent individually.
The receiving end checks that all packets arrive, and are intact, asks for
repeats of missing or damaged packets, and reassembles the message.
So the level above doesn't have to worry about reliably sending messages,
and can just send messages.
Meaning
A yet higher level is responsible for what the bits 'mean'. Depending on the
context, a particular group of bits might represent the letter 'x', or
represent the colour of a pixel in an image.
The User
And a yet higher level is responsible for intermediating with the user,
dealing with requests for information (e.g. the click on a link), and receiving
and displaying the results.
So each level has a different set of responsibilities, and a different set
of semantics, but builds on the lower layers.
Identity and Security
All those layers I have described are about messages, or documents.
But one question is where to put 'identity', the indication of who you are,
so that responding machines can determine what you are allowed to see.
And the other side of the same coin: where to put 'security', how to stop
other people knowing more about you than you want.
Where to Put Identity and Security
Very early versions of the internet protocols (I'm talking about the 1960's
here) had planned to put some aspects of this in a very low level of the
internet stack.
You can argue that this is a good place for it: to connect to the internet,
you have had to log in to your computer; your computer knows it really is you.
Identity should be transitive: you shouldn't have to repeatedly identify
yourself.
The Price of Identity and Security
However, at that time, it was deemed too expensive (and I suspect that
hardware wasn't really powerful enough to support it).
So they left it out.
The mistake they made was not leaving the hooks so that it could be added
later, when computers would become cheaper and more powerful.
The Cost of No Identity and Security
The early internet was used in academic environments, and identity and
security were deemed less important. They didn't anticipate spam...
So identity and security ended up as an afterthought.
Where Identity and Security ended up
Where did it all end up getting put? Right at the top of the stack of
layers, in the application layer, or just underneath.
This is why Google is now forcing everyone to use https, adding the security
aspect at the web connection level.
And why every damn website where you can log in asks for a password, adding
identity separately to each website.
Is this too late to fix?
Public Key Cryptography
Everyone has two matched keys:
- One is public: anyone can get a copy.
- One is private: only you have it.
- You can lock a message with either key, making it unreadable.
- If you lock with one key, only the other key can open
it.
('Keys' are very large numbers, 300 digits or more; 'locking' means
scrambling the message using those large numbers)
Identity
I lock a message with my private key (so it can only be
opened with my public key).
I send the locked message to you.
You get a copy of my public key: if it opens the message,
you know it was really from me.
No more spam!
Privacy
I lock a message with your public key (so it can only be
opened with your private key).
I send you the locked message: I know that only you can open it to read
it.
Secure messaging
Combine those two things:
I lock a message:
- once with my private key,
- and a second time with your public key.
I send it to you:
- you know it's really from me
- only you can read it.
Public keys for passwords
We can use the same process instead of passwords when logging in to
websites.
Registering with a site
You want to create an account at an online shop. You click on the "Create an
account" button.
The site asks you to for a username, which you provide, and click OK.
The site checks the user name is free, and sends a message to your browser
that you want to register.
The browser asks if you want to register. You click Yes.
The browser and the site exchange public keys.
Logging in to a website
You fill in your username, and click on Log in.
The site sends a random message to your browser, locked with the public key
it has registered for that username, and locked with its own private key. It
asks your browser to tell it what the message is.
Your browser knows it is really from the site (and not someone
pretending).
The browser asks if you really want to log in with that username, and if so
decodes the message and sends it back, this time locked with your private key
and the site's public key.
The site therefore knows it is really you and lets you in, without typing in
a password!
Anonymity
The other side of the identity coin is anonymity.
The internet was founded on anonymity, and that was seen as a good thing.
However, there are some bad aspects: the rudeness in comments (and the
trolls, and the bots) can be traced back to anonymity,
Nevertheless, you don't want to have to identify yourself every time you go
to a website, and you don't want companies (or governments) following your
every move on the web.
Are we really anonymous?
We all know about cookies.
Cookies are small pieces of information deposited on your computer by
websites that they can read later.
But even without cookies, we can be tracked using several techniques.
Identification
At work once, we were given a questionnaire to fill in that we were
guaranteed was anonymised.
Unfortunately the first two questions were:
- What is your nationality
- How old are you?
These two questions would have uniquely identified me. I didn't fill it
in.
Identification
In fact 85% of US citizens are uniquely identifiable by postcode+date of
birth+gender.
I expect that the percentage is even higher in the Netherlands, since the
postcode is more specific here.
Similarly with browsers: your IP, plus certain other discoverable aspects of
your computer can uniquely identify you: they often don't even need cookies.
Where is Donald Trump?
A recent article in the New York TImes showed that they could acquire an
'anonymised' dataset of 50 billion mobile phone positions, of 12 million
people.
Within minutes they located 'down to a few feet' where Donald Trump had
been, where his security personel live, and the routes they take between home
and work, and using that could discover the security personel's names and
family details.
The data came from a location data company, one of dozens quietly collecting
precise movements using software slipped onto mobile phone apps - anything from
weather apps to local news apps to coupon savers.
How
to track Donald Trump
Tracking Pixels
Many sites, and emails, use a technique of including a tiny (one
pixel) image.
That gets loaded from a server somewhere, that then records that you have
visited that site, or opened that email, and from where, and how many
times...
Google advertises this as a service so you can see how many people visit
your site and where from. It also allows Google to track individuals as
well...
Internet of Things
 Not particularly new [e.g.
petrol stations], but now more widely distributed.
Not particularly new [e.g.
petrol stations], but now more widely distributed.
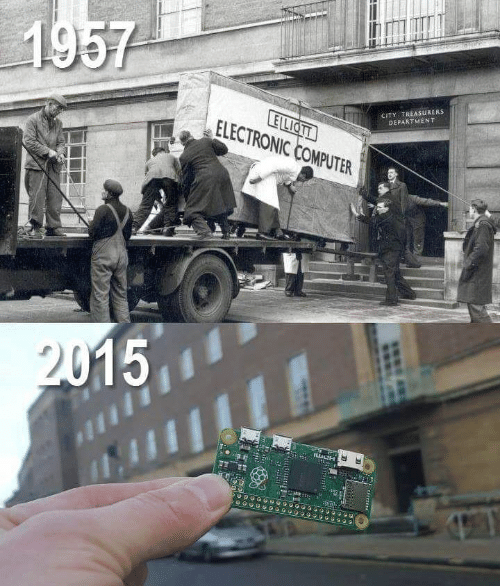
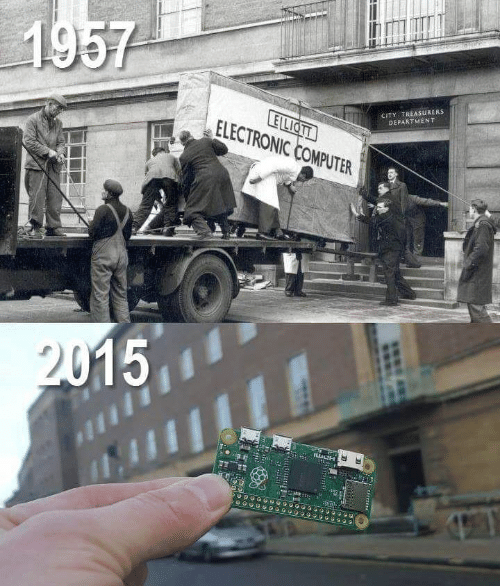
Enabled by the dramatic lowering of cost of computers, and their rising
power.
The Raspberry Pi is 1 million times faster than the Elliott, one millionth
of the price, and one two-millionth the size.
Security and privacy
So slowly but surely more and more things are getting connected to the
internet.
Connected now: central heating, lights, doorbells [leaking information],
cars. Toys.
But... the computers were not powerful enough to do proper security.
Security and privacy
So slowly but surely more and more things are getting connected to the
internet.
Connected now: central heating, lights, doorbells [leaking information],
cars. Toys.
But... the computers were not powerful enough to do proper security.
George Santayana:
Those who cannot remember the past are condemned to repeat
it.
Security and privacy
So slowly but surely more and more things are getting connected to the
internet.
Connected now: central heating, lights, doorbells [leaking information],
cars. Toys.
But... the computers were not powerful enough to do proper security.
George Santayana:
Those who cannot remember the past are condemned to repeat
it.
Pemberton's Corollary:
Those of us who CAN remember the past are condemned to watch
others repeat it...
Other Examples of Insecurity
Someone
broke into a casino, via an aquarium.
Someone
shows how to break into a car, via the internet-connected radio, and
completely take over the control of the car.
Conclusion: internet connected devices are not safe. Once you've got in, you
have access to far more devices, because devices are trusted behind the
firewall.
Advice:
keep your internet of things devices on a different network to your
computers.
Meet my grandfather
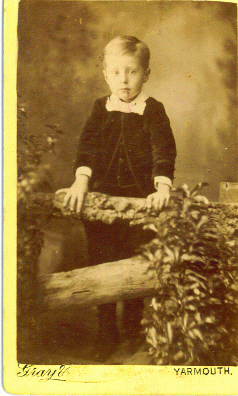
Born in 1880, a middle child in a family of 20(!) children.
1880: nearly no modern technologies; only trains and photography. No
electricity.
In such a large household, as is to be expected, each child had a task, and
it was my grandfather's to ensure that the oil lamps were filled.
It must have been indeed an exciting time, when light became something you
could switch on and off.
This may well explain my grandfather's fascination with electricity, and why
he set up a company to manufacture electrical switching machinery.
Paradigm shifts
Trains and photography were paradigm shifts: they change the way that you
think about and interact with the world.
But they often replace existing ways of doing things, taking companies with
them.
1609
 1609, an Englishman, Henry Hudson, working for a Dutch
company, discovering the island of Manhattan. Then, and for centuries after,
all trans-Atlantic shipping was done with sailing ships.
1609, an Englishman, Henry Hudson, working for a Dutch
company, discovering the island of Manhattan. Then, and for centuries after,
all trans-Atlantic shipping was done with sailing ships.
Steam ships
 The Fighting Temeraire tugged
to her last Berth to be broken up, by Turner, 1838
The Fighting Temeraire tugged
to her last Berth to be broken up, by Turner, 1838
(The Temeraire was an important sailing ship from the Battle of Trafalgar
1805.)
When steam ships were introduced they were not reliable enough to travel
trans-Atlantic distances, they couldn't travel far without breaking down, and
they were inclined to blow up.
Niche
But steam ships were able to find a niche in lake and river transport, where
the distances were short, and where they had the advantage of being able to
travel against the wind and on wind-still days.
Once in the niche they could improve reliability until they were
able to travel trans-Atlantic.
Once that happened, all shipping switched to steam, and all the companies
producing trans-Atlantic sailing ships went out of business; not one survived
into the 20th century.
Modern example: Kodak
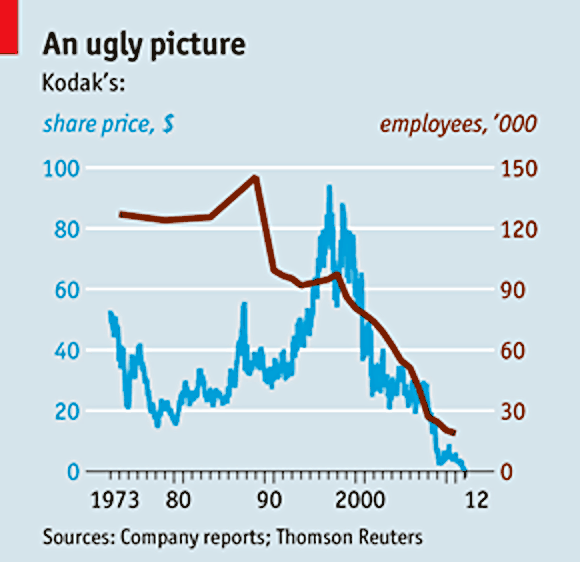 Who would have thought that Kodak didn't see this coming?
Who would have thought that Kodak didn't see this coming?
Paradigm shifts have a long history
From Lorna Doone (taking place around 1700):
"The roads are much improved, and the growing use of stage waggons
(some of which will travel as much as forty miles [64 km] in a summer day)
has turned our ancient ideas of distance almost upside-down"
1820

Accelerating change
Going back to my grandfather.
He was born in a world of only two modern technologies, but in his life of
nearly a hundred years, he saw vast numbers of paradigm shifts:
electricity, telephone, lifts, central heating, cars, film, radio,
television, recorded sound, flight, electronic money, computers, space
travel, ... the list is enormous.
We are still seeing new shifts: mobile telephones, cheap computers that can
understand and talk back, self-driving cars, ...
Does that mean that paradigm shifts are happening faster and faster?
Yes.
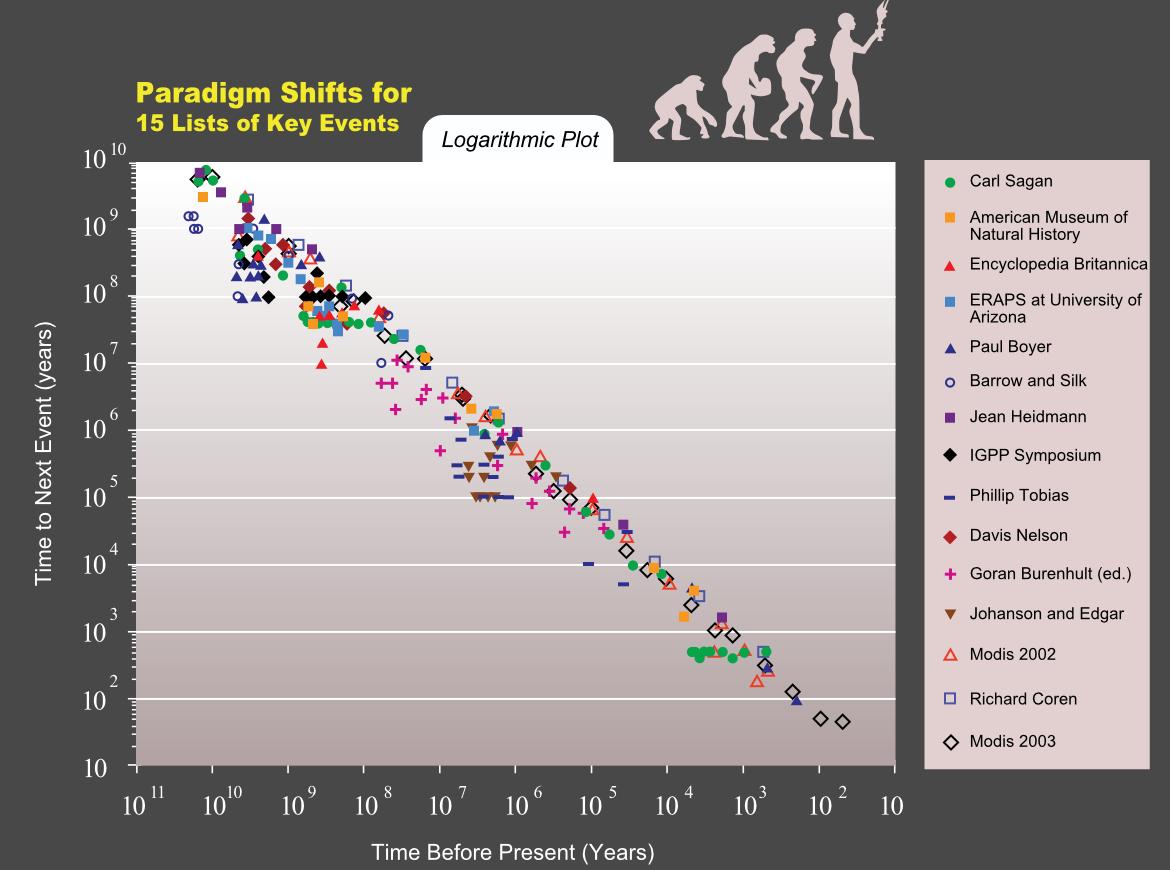
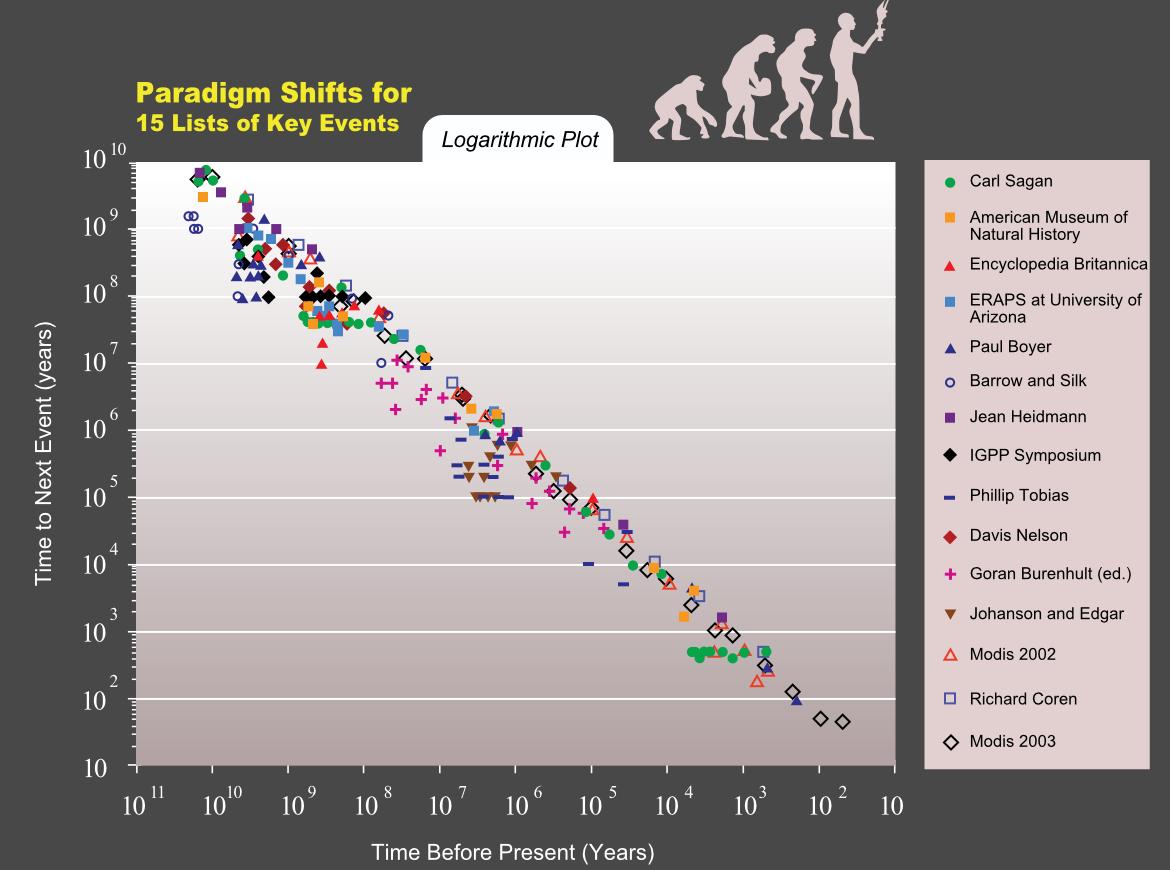
Kurzweil did an investigation, by asking representatives of many different
disciplines to identify the paradigm shifts that had happened in their
discipline and when. We're talking here of time scales of tens of thousands of
years for some disciplines.
He discovered that paradigm shifts are increasing at an exponential
rate!
If they happened once every 100 years, then they happened every 50 years,
then every 25 years, and so on.
Acceleration
Year Time to next =Days
0 100 36500
Acceleration
Year Time to next =Days
0 100 36500
100 50 18250
Acceleration
Year Time to next =Days
0 100 36500
100 50 18250
150 25 9125
Acceleration
Year Time to next =Days
0 100 36500
100 50 18250
150 25 9125
175 12.5 4562.5
Acceleration
Year Time to next =Days
0 100 36500
100 50 18250
150 25 9125
175 12.5 4562.5
187.5 6.25 2281.25
193.75 3.125 1140.63
196.875 1.563 570.31
198.438 0.781 285.16
199.219 0.391 142.58
199.609 0.195 71.29
199.805 0.098 35.64
199.902 0.049 17.82
199.951 0.024 8.91
199.976 0.012 4.46
199.988 0.006 2.23
199.994 0.003 1.11
199.997 0.002 0.56
A Similar Acceleration
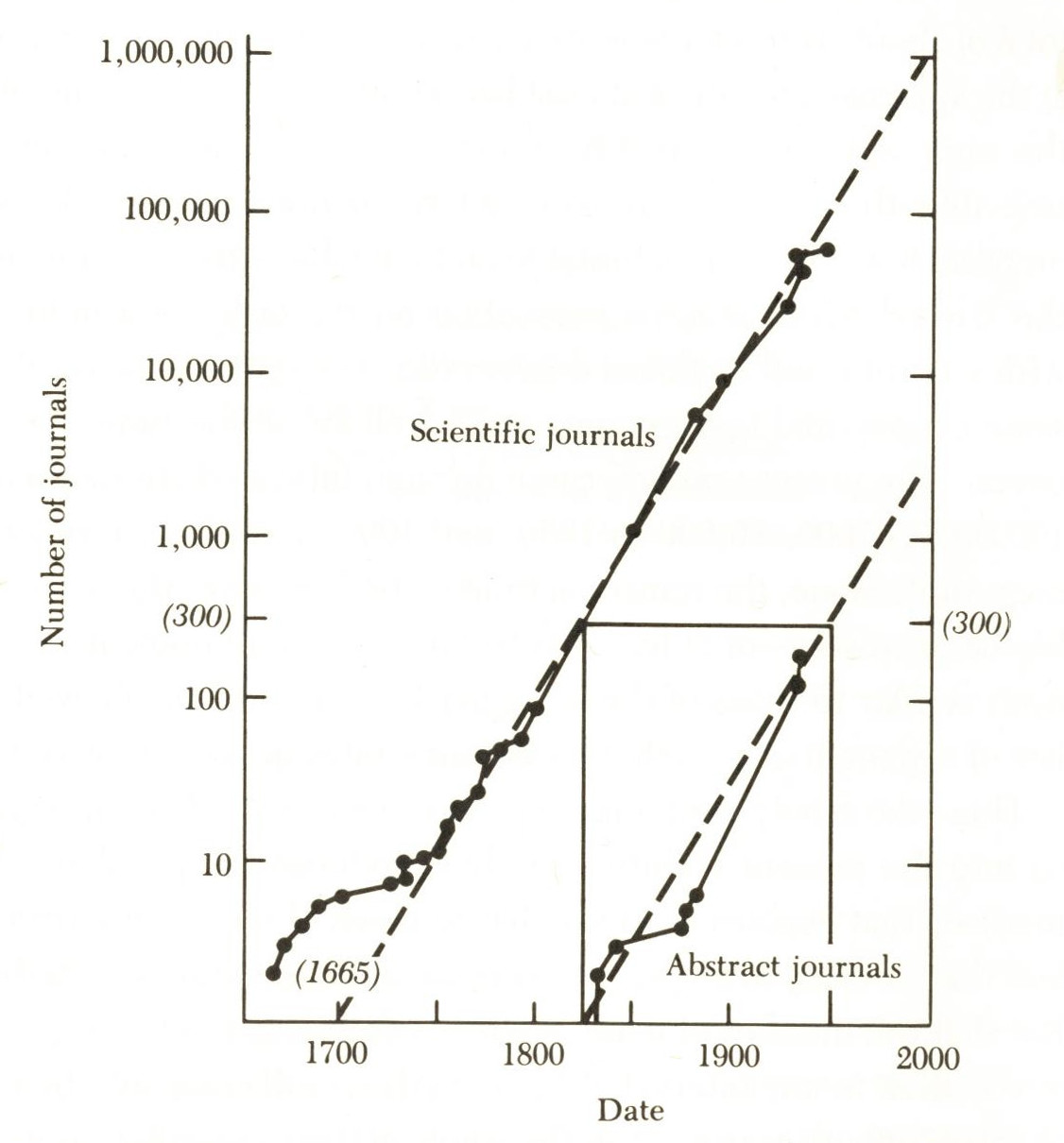 That may seem impossible,
but we have already seen a similar expansion that also seemed impossible.
That may seem impossible,
but we have already seen a similar expansion that also seemed impossible.
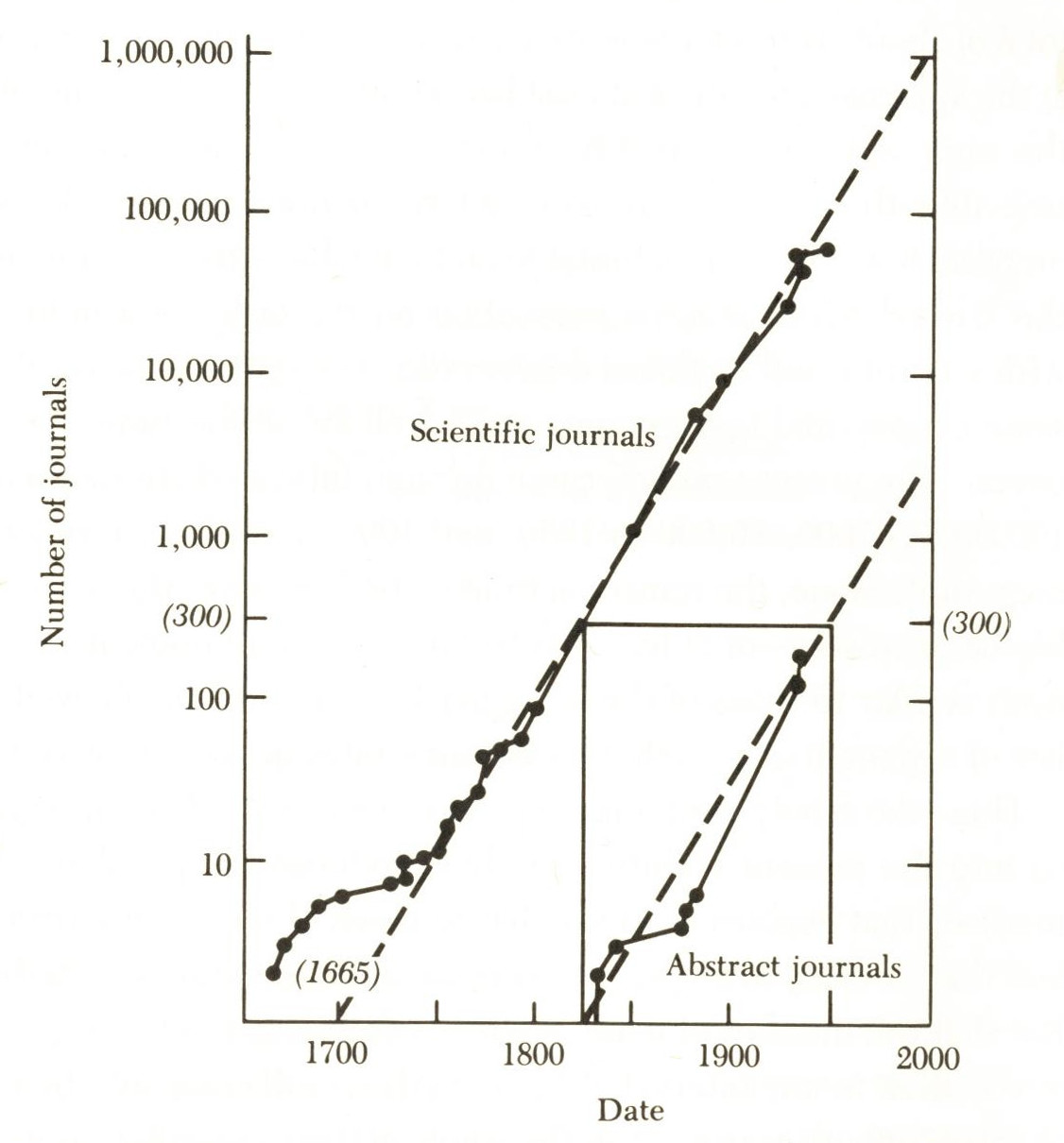
In the 1960's we already knew that the amount of information the world was
producing was doubling every 15 years, and had been for at least 300 years.
We 'knew' this had to stop, since we would run out of paper to store the
results.
And then the internet happened
How?
So sometime in the nearish future paradigm shifts will apparently be
happening daily? How?
One proposed explanation is that that is the point that computers become
smarter than us: computers will start doing the design rather than us.
The Looming AI Crisis
 What if computers are no longer in our service?
What if computers are no longer in our service?
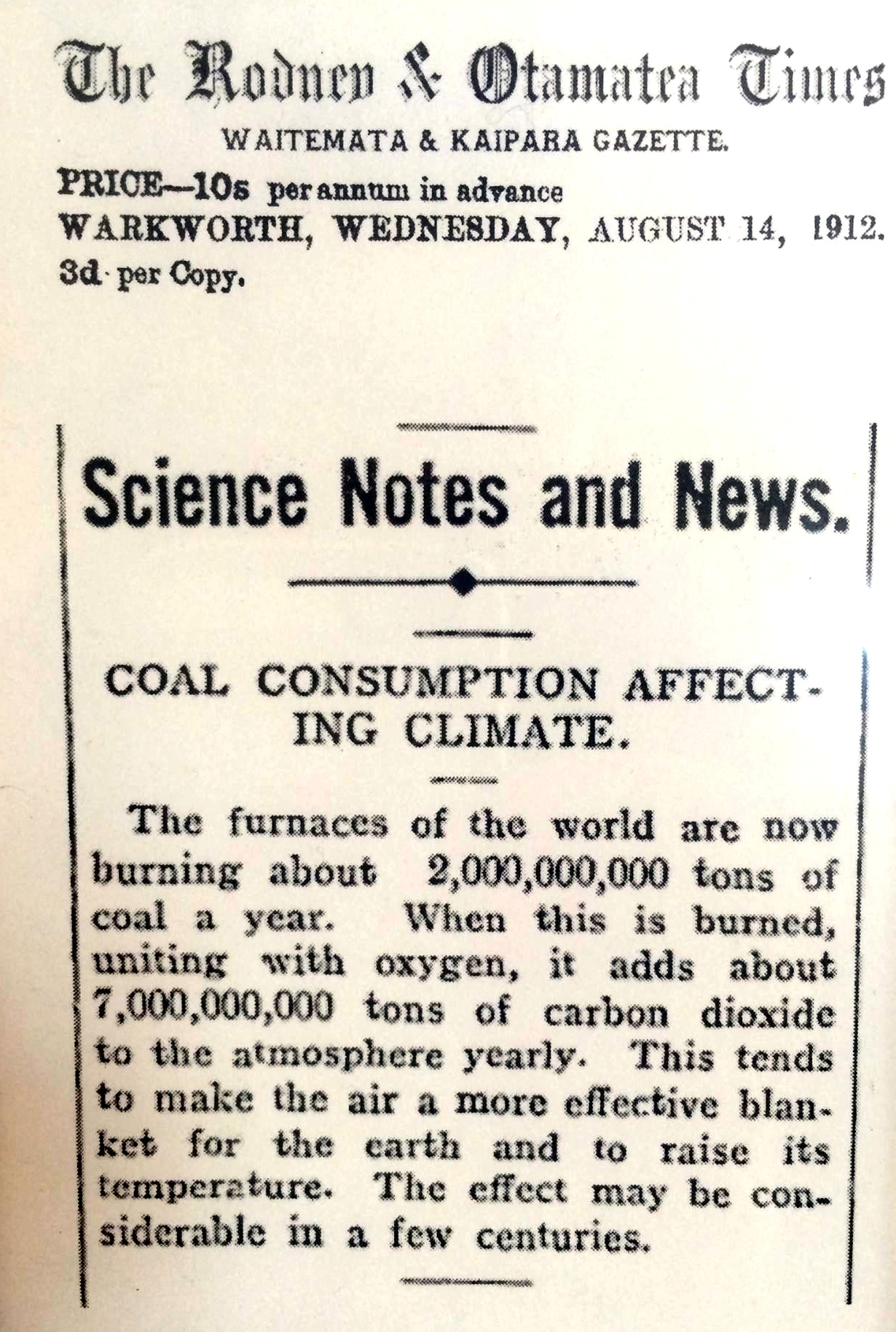
What if they are no longer in our service and spot the cause of the climate
crisis.
We need to plan.
But we respond very slowly, look at Kodak, look at climate change...
Conclusion
Humans are dreadfully bad at avoiding crises.
The question is, which will get us first: the climate crisis or the AI
crisis?
Sorry
 Not particularly new [e.g.
petrol stations], but now more widely distributed.
Not particularly new [e.g.
petrol stations], but now more widely distributed. 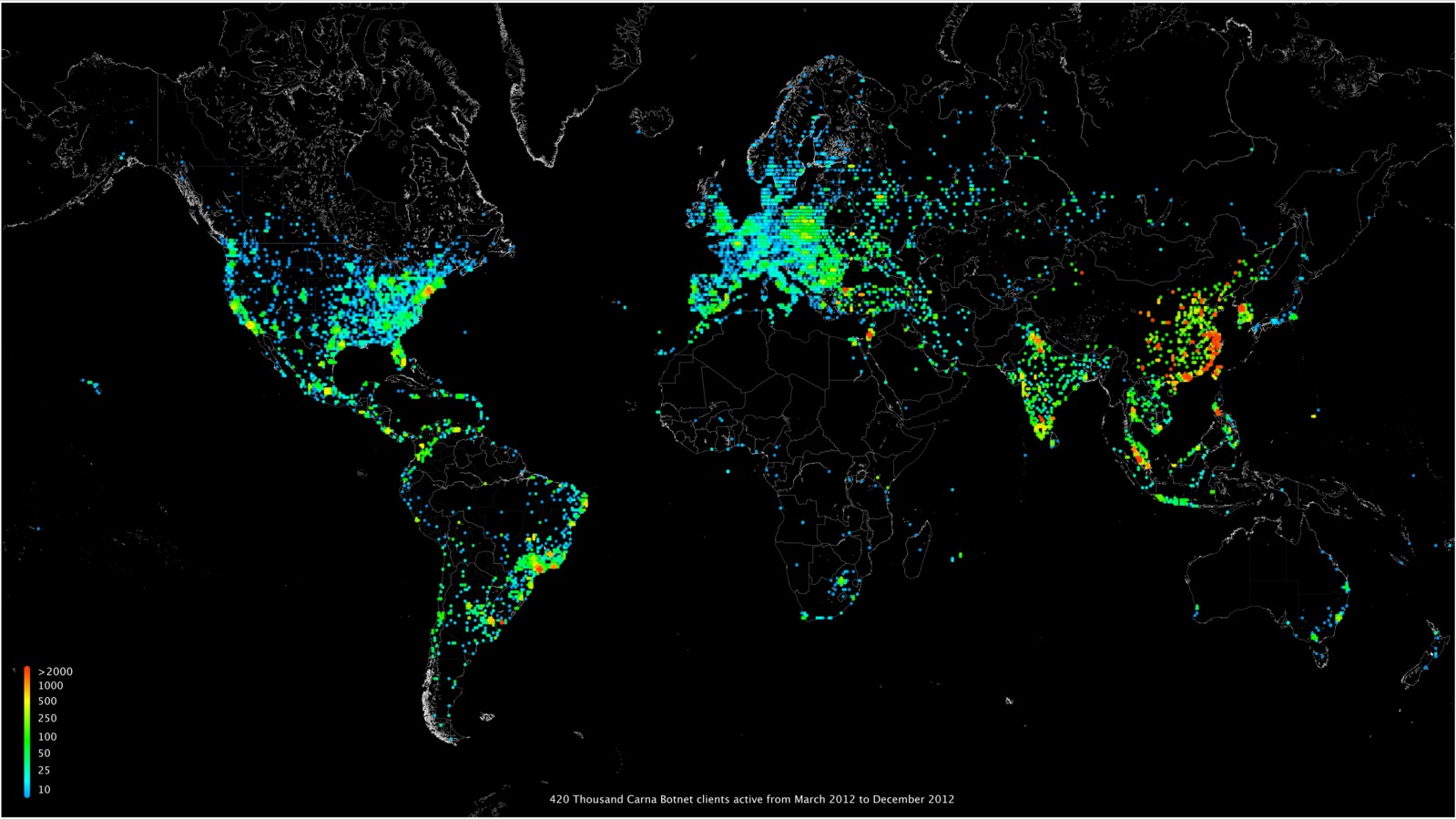
 1609, an Englishman, Henry Hudson, working for a Dutch
company, discovering the island of Manhattan. Then, and for centuries after,
all trans-Atlantic shipping was done with sailing ships.
1609, an Englishman, Henry Hudson, working for a Dutch
company, discovering the island of Manhattan. Then, and for centuries after,
all trans-Atlantic shipping was done with sailing ships. The Fighting Temeraire tugged
to her last Berth to be broken up, by Turner, 1838
The Fighting Temeraire tugged
to her last Berth to be broken up, by Turner, 1838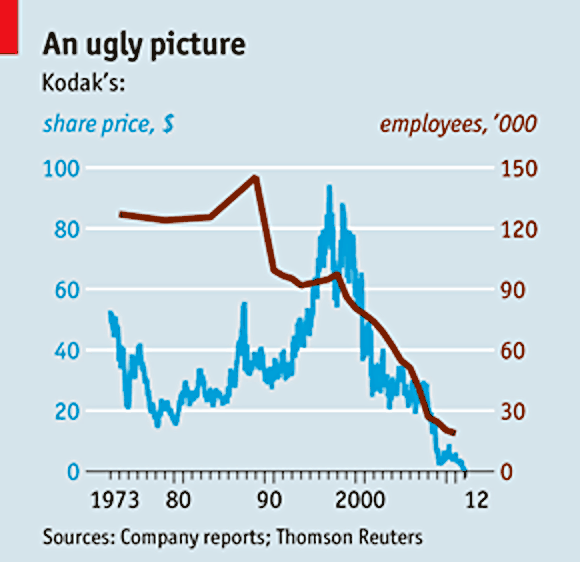 Who would have thought that Kodak didn't see this coming?
Who would have thought that Kodak didn't see this coming?
 That may seem impossible,
but we have already seen a similar expansion that also seemed impossible.
That may seem impossible,
but we have already seen a similar expansion that also seemed impossible. What if computers are no longer in our service?
What if computers are no longer in our service?